3-D printers’ sounds hold secrets that can be stolen, UCI researchers find
- Share via
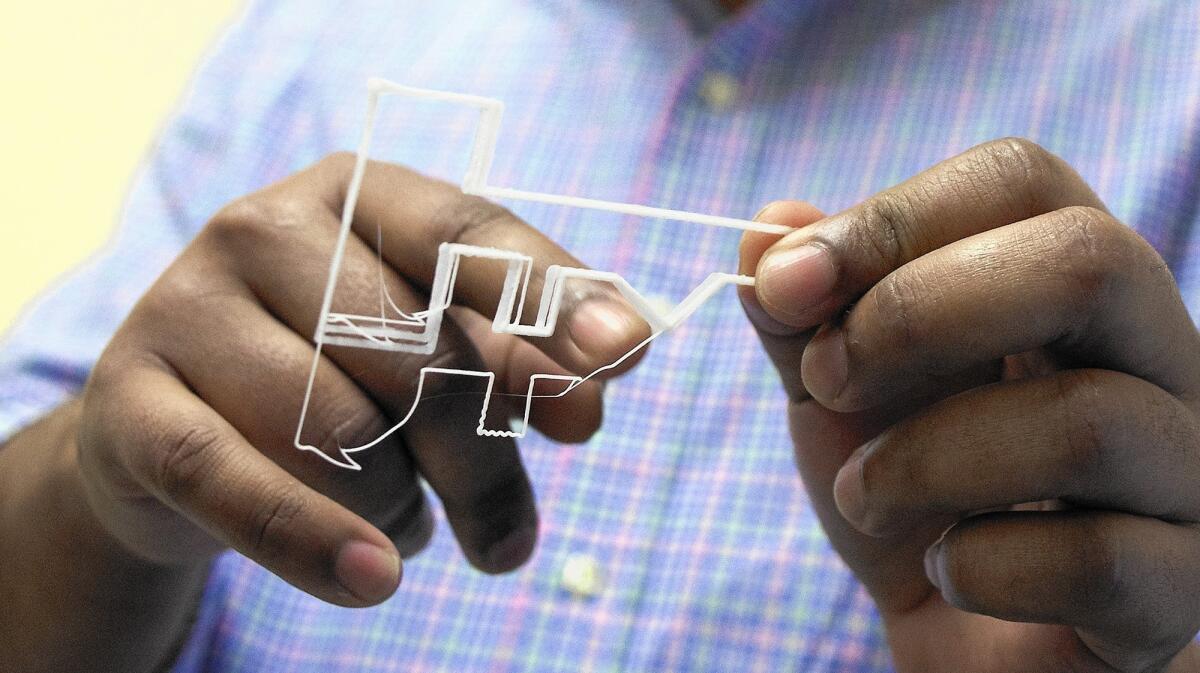
A 3-D printer in a UC Irvine research lab creates an object shaped like a key. With the machine’s every precise movement, a sound is made.
UCI researchers decided to record those sounds and found that by processing the acoustic signals alone, they could reprint the key nearly exactly.
“The key is small, but the implication is huge,” said Mohammad Al Faruque, director of UCI’s Advanced Integrated Cyber-Physical Systems Lab. “It means that valuable processing information can be lost” to hackers who, for example, might capture audio from the printing process to make parts for cars and planes.
“For a company, the prototyping stage is critical and you don’t want that information to be leaked,” said Sujit Rokka-Chhetri, a student on the research team. “Because of that, it’s important to find these ways that information can be breached.”
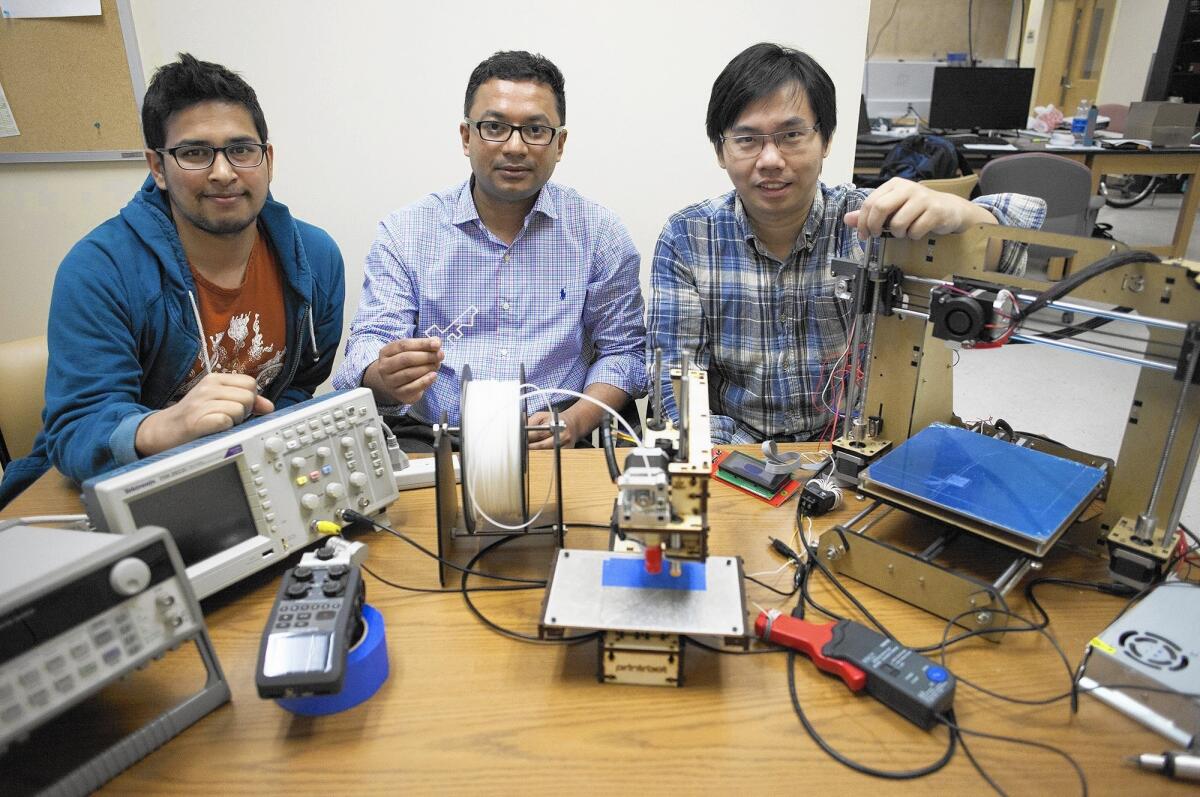
Since last summer, Al Faruque and a group of graduate students at UCI have studied 3-D printing and how the machine’s emanations can reveal sensitive information.
3-D printing systems produce objects using a source code, which contains information the printer can use to build the layers of the object.
Though strong encryption can protect the code from being stolen, “in a 3-D printer, there are a lot of emissions in the form of sound and vibrations,” Al Faruque said. “The question was: Does all of this energy have a footprint, and by having that, can we access the system?”
During its research, the team had a 3-D printer create a key out of polymer plastic.
The researchers used an audio recorder to capture the sounds of the printer as it shifted back and forth to make the object.
“With sound, we can understand what direction the printer is moving and at what speed,” Al Faruque said.
Using an information processing algorithm, the team was able to use only the sounds to produce the code needed to print almost the exact same key.
According to Al Faruque, a device as common as an iPhone could record the sounds made by a 3-D printer.
Though sounds can leak processing information, trying to build a silent printing system wouldn’t be the smartest or most cost-efficient solution, the team believes.

The researchers plan to look into other ways information can be protected.
“You could write the code in such a way where people would get confused if they tried to access it or make it so that the sound is disguised,” Rokka-Chhetri said. “Somehow, you can try to hide the information.”
Al Faruque and Rokka-Chhetri will travel to Vienna, Austria, in April to present their team’s findings at the International Conference on Cyber-Physical Systems, a gathering of professionals from engineering, mechanical and related disciplines.




