After Sony hack, Justice Department creates office to help companies stop cyberattacks
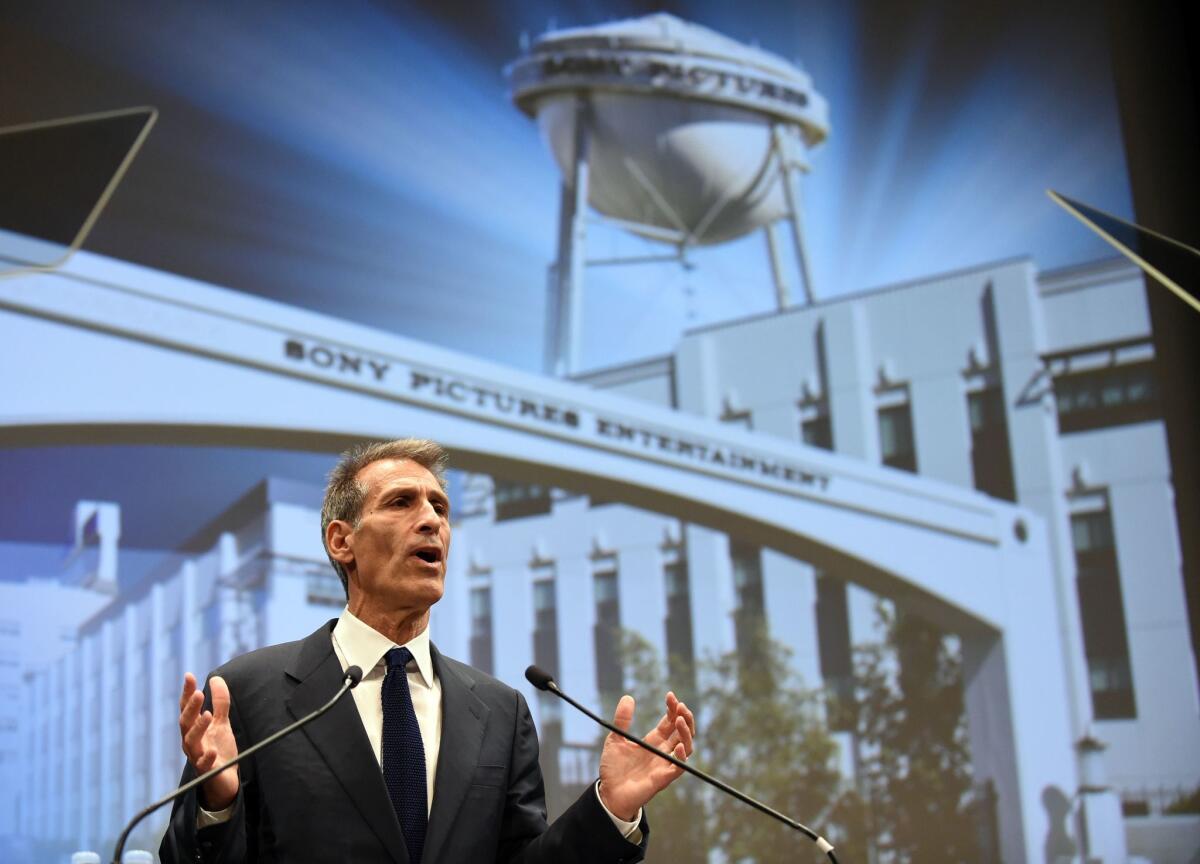
Michael Lynton is the chief executive of Sony Pictures Entertainment, which last year suffered a devastating cyberattack by North Korea. The U.S. Department of Justice has created a new office to help companies prevent attacks and respond when they happen.
- Share via
Reporting from San Francisco — North Korea’s cyberattack on Sony Pictures Entertainment last November was a “catalyzing event” that pushed the U.S. government to bulk up protections for corporations against nation-state cyberattacks, a top Department of Justice official said.
“We had started to move to confront the cyber espionage threat,” said John Carlin, assistant attorney general at the Justice Department for national security. “But a major rogue destructive act by a nation state against an entertainment company? We weren’t thinking about that.”
The Justice Department has created a new office to help companies prevent attacks and respond when they happen, although significant funding remains gridlocked in President Obama’s proposed budget, he said Tuesday at Vanity Fair’s annual New Establishment Summit.
Carlin was joined on stage by Sony Entertainment Chief Executive Michael Lynton. Their talk was something of a casual autopsy of the hack, which was traced back to North Korea.
The hackers destroyed two-thirds of the Sony division’s servers while leaking personal information on employees and their families as well as embarrassing emails between Sony executives and movie stars.
Although Lynton again criticized the media for publicizing those “salacious” emails, he said the attention did serve a purpose: “If they had hacked General Electric or somebody like that and published those emails, I don’t think the American public would have paid quite the attention they did.”
Carlin said the Justice Department is starting to take a preventive approach to corporate cyberattacks, helping companies develop defenses and warning them about possible attacks.
“It is our firm determination to tell private companies when we discover intrusions,” he said. And “we’re ... not just showing up on the doorstep of a company and saying, ‘You’ve been hacked. Good luck.’”
When an attack occurs and the perpetrators can be identified, he said, “offense has to way-outstrip defense.”
Options include military action if there’s “loss of life or critical infrastructure,” economic sanctions or prosecuting foreign nationals for cybercrimes. Last year, the Justice Department indicted five hackers from the Chinese military for allegedly stealing intellectual property from U.S. companies in the steel industry. Those hackers remain at large.
Some critics say that although the Justice Department is moving in the right direction, its commitment falls far short of what’s needed.
“The reality is that companies can hardly get anyone to call them back when they have an incident because [authorities are] too busy,” Jody R. Westby, chief executive at Global Cyber Risk, told Carlin from the audience. “And dollar limits are going to be a big factor.”
How much budget money the DOJ gets for the new initiatives will determine whether serious action will follow all the talk, Westby said.
Lynton praised the FBI, part of the DOJ, for its cooperation after the North Korea attack — both in identifying the perpetrator, and helping employees deal with the theft of their personal information.
Sony was able to quickly get the FBI’s attention because of its connections in Washington, D.C., Lynton said. A top Sony executive “immediately called into the FBI and knew who to call,” he said.
Acknowledging that not all companies have such access, Carlin recommended corporate executives “pick a person” to establish a relationship with. “It could be the local U.S. attorney, it could be the head of the FBI there, it could be us at the DOJ.”
Twitter: @russ1mitchell







