WeChat and other iOS apps infected after developers turn to tainted programs
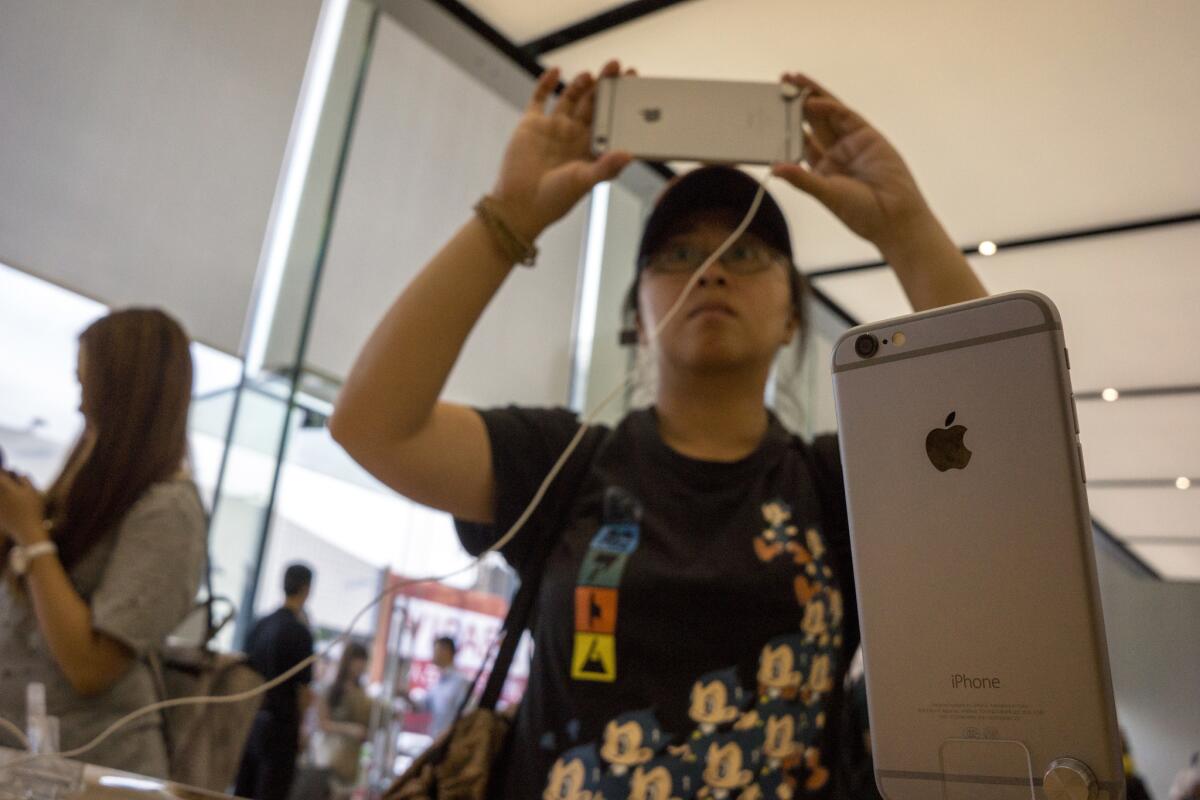
Chinese customers try out iPhones at the Apple store in Hangzhou, China.
- Share via
App developers who downloaded key Apple software from somewhere other than the company’s App Store inadvertently stuck viruses into several big-name apps, mostly in China.
The iPhone, iPod and iPad apps laden with malicious code allow hackers to send people to counterfeit websites, where usernames and passwords could be harvested, or access data that are being copied and pasted.
Messaging app WeChat, Chinese ride-hailing app Didi Kuaidi and contacts app CamCard were among those affected, cybersecurity company Palo Alto Networks reported last week. Apple acknowledged the issue over the weekend, putting the blame on unauthorized copies of its free app development program Xcode. The incident highlights the risks of unofficial app stores and the Internet system in China.
Chinese software developers might have searched the Web for Xcode after deciding that the App Store download was taking too long, Palo Alto Networks said.
Apple only recently began storing data on servers in China, a move that makes accessing photos, movies and documents much quicker for the millions of people in China who are taking up the iPhone. Apple didn’t immediately say whether it also stores apps in China, but generally downloads are slow because of China’s distance from the company’s servers and the country’s extra firewalls.
SIGN UP for the free California Inc. business newsletter >>
Installing the modified versions of Xcode floating around online would have been simple -- just requiring a quick security setting change. But as apps built using the fake versions reached the App Store, malicious code secretly passed within them, potentially affecting hundreds of millions of consumers. In WeChat’s case, a spokeswoman said a preliminary investigation found no user information was compromised. Version 6.2.6 of the app is not affected.
A security researcher compared bypassing the official app store to jaywalking.
“Most of the time, everything turns out fine,” Tod Beardsley, security research manager at Rapid7, said in a prepared statement. “It’s not that developers are dumb and don’t know the risks; they simply consider the risk extremely unlikely, and if it’s slightly more convenient to ignore one or two security best practices, they will proceed accordingly.”
Chat with me on Twitter @peard33.
MORE FROM TECHNOLOGY
An obscure battle over wireless airwaves comes to Trojan football
China’s Renren leads $15.5-million investment in L.A. start-up Aspiration
Disney leads $65-million investment into virtual-reality film company Jaunt