L.A. County targeted in phishing cyberattack; private information of 750,000 people compromised

- Share via
Confidential health data or personal information of more than 750,000 people may have been accessed in a cyberattack on Los Angeles County employees in May that led to charges this week against a Nigerian national, officials have disclosed.
The May 13 attack targeted 1,000 county employees from several departments with a phishing email. The message tricked 108 employees into providing usernames and passwords to their accounts, some of which contained confidential patient or client information, officials said.
Most of the 756,000 people whose information may have been accessed had contact with the Department of Health Services, according to the county. A smaller amount of confidential information from more than a dozen other county departments also was compromised.
Among the data potentially accessed were names, addresses, dates of birth, Social Security numbers, financial information and medical records — including diagnoses and treatment history — of clients, patients or others who received services from county departments.
Officials said there is no evidence that confidential information has been circulated, sold or released.
The county learned of the attack the day after it happened, and officials said they responded with security measures and a criminal investigation. But the county waited more than seven months to inform the public, citing an exemption under state law that allows delayed notification to protect ongoing investigations.
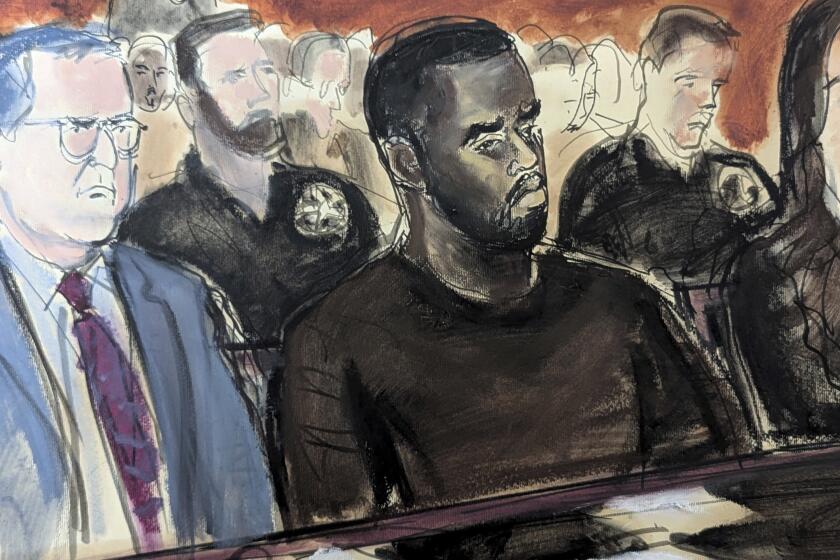
Cyber investigators with the L.A. County district attorney’s office traced the attack to Nigeria. Prosecutors issued an arrest warrant Thursday, accusing Austin Kelvin Onaghinor, 37, of launching the attack and charged him with nine felony counts, including unauthorized computer access and identity theft.
Dist. Atty. Jackie Lacey said in a statement, “My office will work aggressively to bring this criminal hacker and others to Los Angeles County where they will be prosecuted to the fullest extent of the law.”
These kinds of phishing attacks are on the rise throughout society — and the County has not been immune from that trend.
— Joel Sappell, L.A. County spokesman
Once charges were filed, county officials began mailing notices Thursday to people whose information may have been accessed.
The county’s Chief Executive Office said it delayed public notification of the attack at the request of the district attorney’s office “to protect the confidentiality of the sensitive, ongoing investigation and prevent broader public harm.”
Notifying the public of the attack earlier “may have hindered” the investigation, the county said in a notice about the data breach Friday.
In response to the attack, officials said they have strengthened security measures on county email accounts and enhanced employee training to guard against a growing number of cyber intrusions.
“These kinds of phishing attacks are on the rise throughout society — and the county has not been immune from that trend,” county spokesman Joel Sappell said in a statement.
In February, officials disclosed that the Department of Health Services had been targeted in a smaller-scale “ransomware” attack, a type of malware that cuts off users’ access to files or threatens to destroy them unless a ransom is paid.
The district attorney’s office said in a news release Friday that its cyber investigation team has protected the county from prior attacks, “has investigated 85 cases, involving hundreds of thousands of potential victims and has resulted in several successful prosecutions and restitution totaling nearly $4 million.”
The county is offering a year of free credit and identity-theft monitoring for people affected by the May phishing attack and has set up a website and call center for those seeking information: (855) 330-6368.
Twitter: @tonybarboza
ALSO
Hollywood hospital pays $17,000 in bitcoin to hackers; FBI investigating
New era begins in L.A. County government as ‘supermajority’ of Democrats takes the helm
Head of L.A. County’s child protective services agency to retire in early 2017
More to Read
Sign up for Essential California
The most important California stories and recommendations in your inbox every morning.
You may occasionally receive promotional content from the Los Angeles Times.