Law Can’t Keep Up With Technology
- Share via
David McOwen thought he was using the Internet for the reason it was created when he installed a computer program that tests the strength of software security. Problem was, the computers he used to run the program weren’t his.
Now McOwen faces a bill for $415,000 and up to 15 years in prison.
His plight illustrates how the law has yet to catch up with technology.
McOwen was once a tech support guy at a state college in Georgia. He loaded up one of those distributed computing programs on hundreds of campus computers and set them loose. Distributed computing lets machines across the Internet work on tiny pieces of one complicated problem, turning those small and weak desktop boxes into one vast and mighty supercomputer. McOwen argues that he was participating in a legitimate research project but admits that he didn’t have the permission of his bosses.
For that, he quit his job to avoid any trouble.
But it didn’t end there. The state of Georgia is hammering out a framework for criminal prosecution. Some people with ties to the government’s case said McOwen’s actions denied system resources--such as space in the network pipes--to other people on the campus who needed those resources to do legitimate, school-approved research.
The attorney general’s office is expected to convene a grand jury later this month that probably will indict McOwen for misuse of government property. Worst case scenario: a felony conviction, a 15-year prison sentence and a bill in the neighborhood of $415,000, which is what Georgia calculates is the cost of network bandwidth used by the distributed computing client at 59 cents a second.
Oh, and he’ll have to pay his own legal fees too.
If the state wanted to scare the bejesus out of McOwen, hey guys, mission accomplished. “To have this come back on me like this, I just don’t have the words,” said McOwen, who says his wife is pretty freaked out about the whole mess. The couple don’t have children. “Thank God. I wouldn’t want to have to put them through this too.”
McOwen, who works today as a wireless telecommunications engineer, insists that he loaded the software on computers on the Clarkston campus of the Dekalb Technical Institute--which has been renamed Dekalb College since he stopped working there in 1999--as an intellectual exercise.
“I’m a scientist at heart,” he said.
The program he loaded came from https://www.distributed.net, and it’s designed to test the security of computer encryption. Encryption scrambles data to keep it safe from prying eyes, but nobody’s really all that sure how solid various types of encryption are.
The Distributed.net program enlists computers all over the world to pound on encryption schemes until the encryption breaks, verifying that the encryption offers reasonable protection, or advertising that the lock somebody is trying to sell doesn’t really work all that well.
The sort of resource sharing illustrated by distributed systems is the basis of the Internet. Computers are on all the time, creating cycles, which can’t be saved. If there’s work around, you can use the cycles. Otherwise, those cycles fade back into the darkness whence they came. Distributed computing is just a way of using computers when there’s no real work being done. Most distributed systems work only when the computer is in screen saver mode.
At the moment, Georgia isn’t buying the one world happy talk view because if the machines under McOwen’s thrall had actually succeeded in breaking the encryption, he would have been eligible for a cash prize from Distributed.net. McOwen, for his part, insists that this was a purely altruistic endeavor, in keeping with the principles the Internet was founded upon.
It seems inevitable that McOwen is going to be made an example of by a bunch of guys who are quite likely to next order that solitaire be removed from all government computers.
I don’t deny that Georgia has a duty to keep people from stealing supplies from government offices. But the digital era calls for a more nuanced approach than is customary. If a government clerk takes home a case of pens, nobody else in the office can use those pens. Absent any claim that somebody was unable to log on to the Dekalb campus network because of the distributed system, my question is: How can anybody claim half a million dollars in harm here?
It used to be that if somebody stole something from me, I’d no longer have access to the stolen good. With digital technologies, somebody can steal something from me--making a perfect copy, for example--and I’d still have the thing.
But they’d have it too. That’s pretty weird.
So it’s not surprising that the law is still trying to figure out how to deal with this kind of situation. I just hope we get it figured out before McOwen goes to the slammer.
*
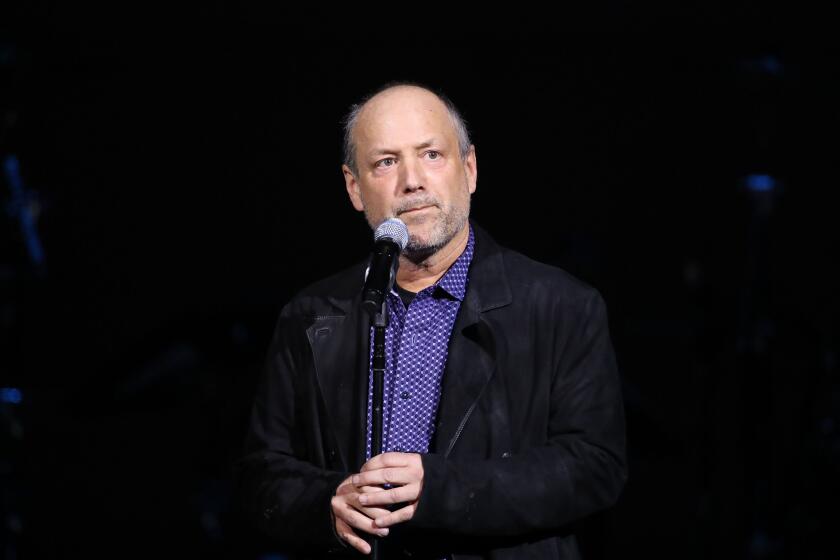
Dave Wilson is The Times’ personal technology columnist.