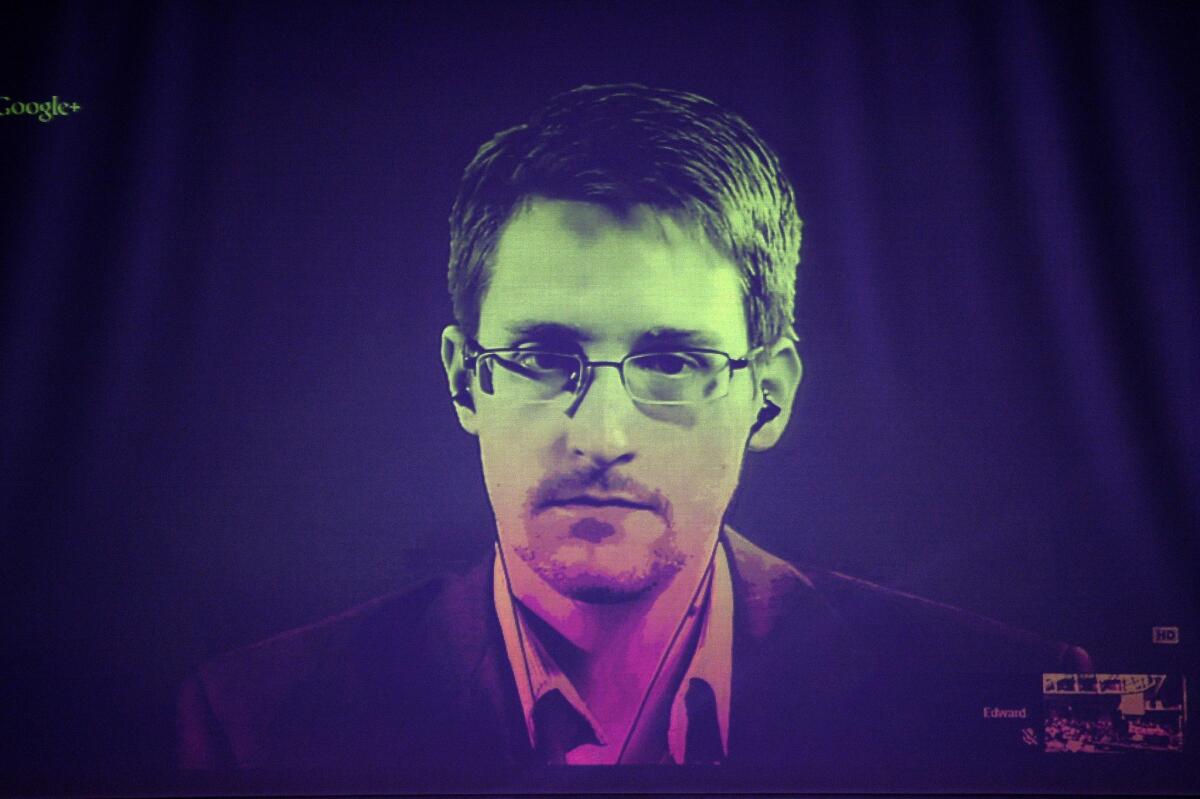
Snowden leaks prompt firms to focus cyber security on insider threats
- Share via
Reporting from Las Vegas — At this week’s Def Con hacker gathering in Las Vegas, Tess Schrodinger sounded almost annoyed.
“The whole insider-threat phenomenon, they act like it’s this new thing,” the cyber security expert told the crowd.
Schrodinger then spent an hour ticking off a long string of insider threats long before Edward Snowden’s famous leaks, from Guy Fawkes, who tried to blow up Britain’s House of Lords, to Brian Patrick Regan, an American Air Force sergeant convicted of trying to sell secrets to Saddam Hussein.
“Suddenly we have to worry about this,” Schrodinger told the Def Con crowd, even citing Judas to make her case. “If you know your history, insider threat has been an issue before the beginning of time.”
But even if insider threats can be traced back to the biblical era, the recent focus on them has had an impact on the business of cybersecurity. Pre-Snowden, much of the attention was devoted to protecting against cybercriminals and foreign hackers. Now companies are increasingly protecting themselves from their own employees. Cracking down too hard can stifle workplace creativity, but potentially losing millions from a single breach of intellectual property can be even more worrisome.
After private companies witnessed the damage a contractor in Hawaii could inflict on the nation’s largest spy agency, they’re lining up to avoid a similar fate. And firms that specialize in protecting corporate data say that’s been a boon.
Verizon’s 2014 threat report, which chronicles breaches in the last year, noted an uptick in internal espionage incidents, not because more necessarily occurred but because an emphasis on “insider-focused” security resulted in more getting detected.
The Snowden news, the report said, “illustrates the risk that exists when an organization must place trust in individuals...Most insider misuse occurs within the boundaries of trust necessary to perform normal duties. That’s what makes it so difficult to prevent.”
Even the former second-in-command at the National Security Agency has benefited.
Chris Inglis, who helps corporations guard against threats as an advisor for data security firm Securonix, said in an interview with The Times that the Snowden leaks have been good for business.
“There isn’t anyone who missed what was happening to or at the NSA last summer,” Inglis said. “Private companies are all trying to defend their slice of the network. ... I think it has heightened their awareness.”
Employees can hack their systems to elevate their login credentials or install malware such as keystroke loggers to get around those controls. And the data thieves aren’t just being paid by rival companies. A large chunk of in-house bad actors are believed to be getting paid off by organized crime.
Bradford Newman, an attorney who focuses on data theft, says he sees companies responding harshly. Some of his clients, including those in professional services and manufacturing, have upped their protections, and for the first time have begun installing defenses on par with those used by military contractors.
“I think there’s a little Snowden freakout,” he said. “There’s a million Snowdens of various degrees at work right now, taking data for profit. ... If you’re working on a product you think is going to generate billions in revenue, you’re going to take that stuff pretty seriously.”
For more tech news, follow @RobertFaturechi







