SEC reveals 2016 hack that may have been used for illegal trades
- Share via
Reporting from Washington — The nation’s top financial markets regulator has revealed that its computer system was hacked last year and that private information might have been used to make “illicit gains” through stock trades.
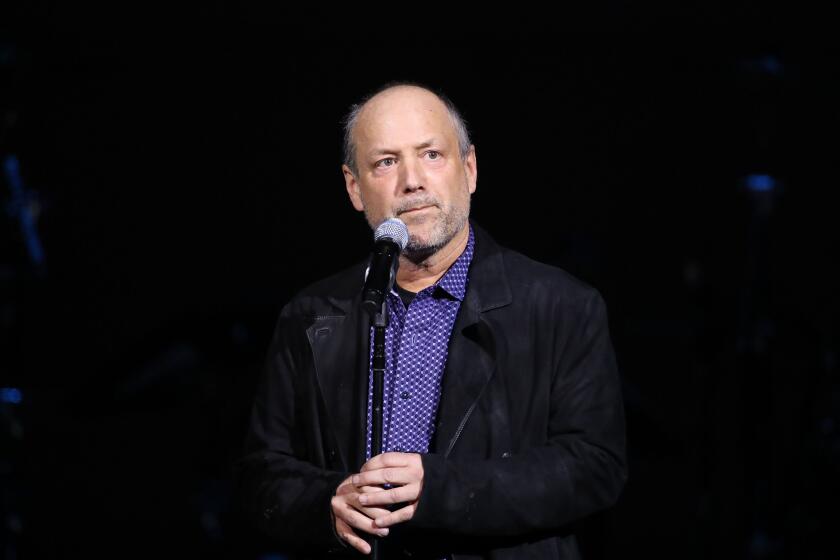
Jay Clayton, chairman of the Securities and Exchange Commission, said in a statement posted on the agency’s website Wednesday night that officials learned last month that the “previously detected” 2016 incident might have been exploited by the hackers for financial gains. The SEC has launched an internal investigation.
The intrusion into the SEC’s EDGAR online database, which companies use to make required securities filings that often contain important financial information, comes on the heels of the revelation by the Equifax credit reporting firm that a hack of its computer system exposed the Social Security numbers and birth dates of as many as 143 million people.
“The SEC’s disclosure, which comes not even two weeks after Equifax revealed that it had been hacked, shows that government and businesses need to step up their efforts to protect our most sensitive personal and commercial information,” said Sen Mark Warner (D-Va.), a leading lawmaker on cybersecurity matters.
Warner said he plans to question Clayton about the incident when he appears before the Senate Banking Committee on Tuesday for a previously scheduled oversight hearing.
The SEC is a repository of massive amounts of information, much of it that companies are required by law to file each quarter. In addition to the EDGAR system, the agency’s enforcement division has information systems with highly sensitive data about investigations of companies, said Matt Rossi, a former SEC official
“Anything that calls into question the security of the information systems at the SEC is obviously the source of significant concern,” said Rossi, a partner at the Mayer Brown law firm in Washington who specializes in cybersecurity matters.
Clayton said Wednesday that the 2016 hack was caused by “a software vulnerability” in the widely used EDGAR system that was “patched promptly after discovery.” The system — an acronym for Electronic Data Gathering, Analysis and Retrieval — processes over 1.7 million electronic filings in any given year, the agency said.
While the EDGAR system is designed to give investors public access to company securities filings, the system has a test-filing option that allows companies to check that their submissions are properly prepared, including having the right security codes, before filing deadlines.
Test filings are not made public and “are routinely removed from the internal system after a short period, generally six calendar days,” according to EDGAR’s manual.
The 2016 hack did not result in unauthorized access to personally identifiable information, jeopardize the SEC’s operations or cause any systemic risk to the financial system, Clayton said.
“Cybersecurity is critical to the operations of our markets and the risks are significant and, in many cases, systemic,” Clayton said.
“We must be vigilant,” he said. “We also must recognize — in both the public and private sectors, including the SEC — that there will be intrusions, and that a key component of cyber risk management is resilience and recovery.”
Rossi said it was ironic that the SEC has been cracking down on investment advisors and broker-dealers for having inadequate cybersecurity protections.
“While the SEC is pushing the industry to adopt increasingly stringent cybersecurity policies and procedures, this is an incident where their own are called into question,” Rossi said. “They might be subject to criticism of ‘Do what we say, not what we do.’”
A July report from the Government Accountability Office found that the SEC had not fully implemented 11 of 58 recommendations spurred by previous audits to secure its computer network, include failing to authenticate users and encrypt sensitive information.
The report also identified 15 new deficiencies that “limited the effectiveness of SEC’s controls for protecting the confidentiality, integrity and availability of its information systems.”
In response to the report, Gregory C. Wilshusen, the agency’s director of information security issues, said in July that the agency was “committed to continuously assessing and strengthening our information security posture.”
Clayton’s statement also mentioned that a 2014 internal review was unable to locate some agency laptops that may have contained confidential information.
The agency also discovered instances in which its personnel used private, unsecured email accounts to transmit confidential information.
The SEC is continuing to investigate the breach and its possible consequences and coordinating with the “appropriate authorities,” according to the statement.
Clayton ordered a review of the SEC’s cybersecurity profile in May 2017, which led to the discovery of the possible illegal trading. The statement did not explain why the hack itself was not revealed when it was discovered last year.
Hackers can use confidential financial information to make money from stock trades before the data is available to the public.
In December, the SEC said it filed suit against three Chinese traders for allegedly using malware to steal emails containing “nonpublic market-moving information” from two New York-based law firms. The traders earned almost $3 million in illegal profits in the first SEC case involving charges of hacking into a law firm’s computer network, the agency said.
And in 2015, the SEC filed an insider trading case against a group of traders who allegedly worked with two hackers in Ukraine to steal corporate earnings news releases from distributors such as PR Newswire before the information was made public.The scheme produced more than $100 million in illegal profits, according to the agency.
ALSO:
Waymo seeks $2.6 billion in damages from Uber for alleged use of one trade secret
Yellen defends Federal Reserve’s bond buying as the central bank starts reducing its stockpile
Redondo Beach halts mixed-use developments after residents raise concerns about traffic
UPDATES:
1:20 p.m.: This article has been updated with comments from former SEC official Matt Rossi.
11:50 a.m.: This article has been updated with details about the Electronic Data Gathering, Analysis and Retrieval system and about other recent hacking-related insider trading cases brought by the SEC.
10:15 a.m.: This article has been updated with Times staff reporting.
This article was originally published at 4:30 a.m.
More to Read
Inside the business of entertainment
The Wide Shot brings you news, analysis and insights on everything from streaming wars to production — and what it all means for the future.
You may occasionally receive promotional content from the Los Angeles Times.