Chinese hackers charged with stealing data from Navy, JPL and U.S. companies
- Share via
Reporting from WASHINGTON — Two hackers associated with China’s main security service were charged with stealing troves of sensitive digital data from the Navy, the Jet Propulsion Laboratory and dozens of U.S. companies as well as American allies overseas, the Justice Department announced Thursday in its latest indictment aimed at suspected Chinese economic and military espionage.
Among other targets, the two hackers allegedly stole confidential data from the Navy, including the names, Social Security numbers, dates of birth, salary information, phone numbers and email addresses of more than 100,000 sailors and other personnel.
They also infiltrated computers linked to NASA’s Jet Propulsion Laboratory in La Cañada Flintridge, the Energy Department’s Lawrence Berkeley National Laboratory in Berkeley and more than 45 companies in at least a dozen states, according to the indictment.
The Trump administration has increasingly complained of what it describes as an alarming surge in sophisticated attacks on U.S. companies and agencies since early 2017 from hackers backed by China’s Ministry of State Security, its chief intelligence service.
Experts say Beijing is trying to steal U.S. technological advances and intellectual property for commercial and military gain. The intelligence agency also seeks to identify people who are spying against it — or whom it potentially can recruit as Chinese spies.
The hacking is a major source of friction between Washington and Beijing as they also spar over punishing trade tariffs, Chinese military expansion in the South China Sea and Chinese-backed infrastructure projects in Africa and Latin America, among other disputes.
While Russia, Iran, North Korea and other adversaries have conducted major cyberattacks on U.S. targets, FBI Director Christopher A. Wray emphasized the Chinese threat as the most pervasive.
“China’s goal, simply put, is to replace the U.S. as the world’s leading superpower, and they’re using illegal methods to get there,” Wray said at a Justice Department news conference Thursday. “China’s state-sponsored actors are the most active perpetrators of state-sponsored espionage against us.”
The hackers also penetrated computers in a dozen other countries, according to prosecutors, and government officials in Britain, Australia and New Zealand accused China of conducting a global cyber-espionage operation in violation of promises Beijing has made in international summits.
“This campaign is one of the most significant and widespread cyber intrusions against the U.K. and allies uncovered to date, targeting trade secrets and economies around the world,” British Foreign Secretary Jeremy Hunt said in London. “These activities must stop.”
U.S. Lt. Cmdr. LizaDougherty, a Navy spokeswoman, declined to comment on the security breach other than to say in a statement that the Navy “takes any incident concerning personally identifiable information very seriously, and ensures that all affected sailors are notified immediately when an incident occurs.”
The indictment, from a federal grand jury in New York, outlines a Chinese operation that was ambitious and audacious in scope.
Industries as varied as aviation, agriculture, banking and finance, telecommunications, consumer electronics, biotechnology, automotive supplies, mining and healthcare were targeted, the Justice Department said.
The companies were not identified, but Wray described them as a “who’s who” of the corporate world.
The alleged cyber thieves worked for Huaying Haitai Science and Technology Development Co. in Tianjin, China, and they “acted in association” with the provincial office of the Chinese Ministry of State Security, the Justice Department said.
Two Chinese nationals, Zhu Hua and Zhang Shilong, were accused of orchestrating “extensive” hacking campaigns that stole hundreds of gigabytes of sensitive data over the last 12 years, according to the Justice Department.
Zhu and Zhang were indicted on charges of conspiracy to commit computer intrusion, conspiracy to commit wire fraud, and aggravated identity theft.
The two are believed to be in China and could not be reached for comment. The Chinese Embassy in Washington did not respond to a phone message seeking comment.
Zhu and Zhang were members of an infamous hacking group known in the cybersecurity community as Advanced Persistent Threat 10, or APT 10, according to prosecutors. The group was also known as Red Apollo, MenuPass and Stone Panda.
Read the Justice Department’s indictment against Chinese hackers »
Prosecutors said that the two hackers steadily improved their ability to breach network defenses in a “continuous and unrelenting effort” to steal software, technology and trade secrets.
In some cases, prosecutors said, they used malware to get access to a digital network, and then to monitor victims’ computers remotely and steal user credentials. The hackers then transferred sensitive data to their own computers using encryption.
Starting in 2014, prosecutors said, the group infiltrated computer networks of service providers that manage information technology for businesses and governments worldwide in an effort to steal “intellectual property and confidential business data on a global scale.”
The group successfully hacked a managed service provider with offices in New York that compromised the data of the provider and clients in a dozen countries involved in banking and finance, consumer electronics, medical equipment and oil and gas exploration, prosecutors said. The service provider was not identified.
In addition to attacks on U.S. targets, prosecutors said the hackers penetrated digital networks at companies in Brazil, Britain, Canada, Finland, France, Germany, India, Japan, Sweden, Switzerland and the United Arab Emirates.
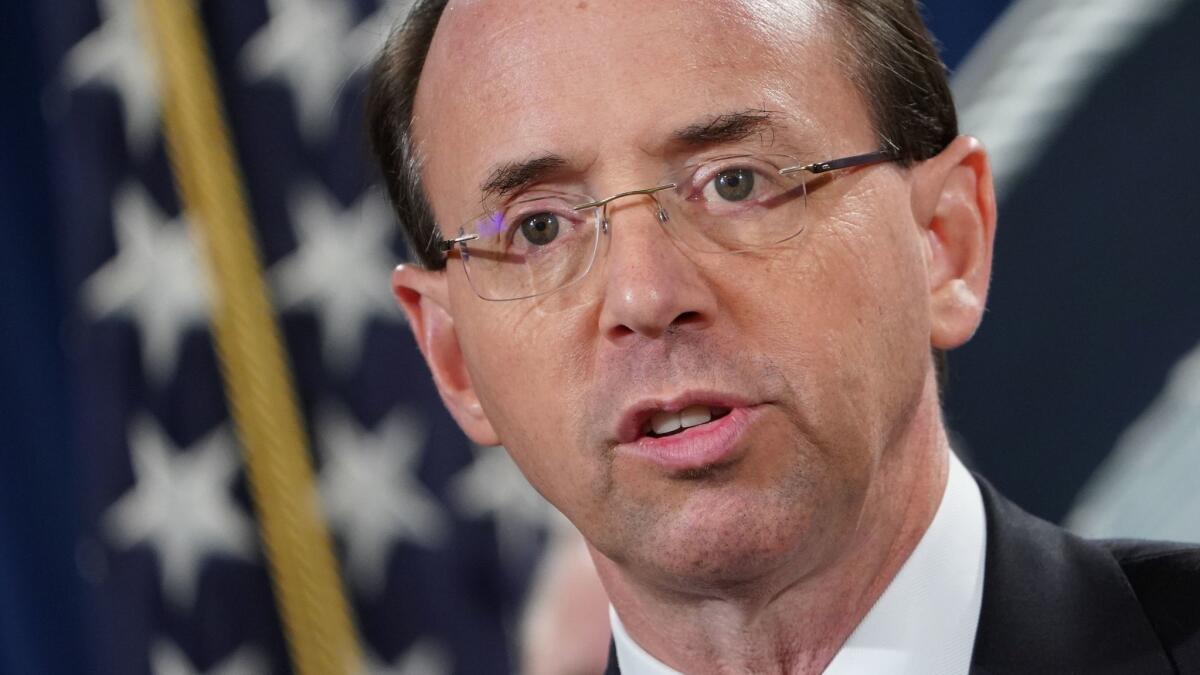
“It is unacceptable that we continue to uncover cybercrime committed by China against other nations,” Deputy Atty. Gen. Rod Rosenstein said at the news conference.
Chinese hacking of U.S. trade secrets has surged since early 2017, according to research by CrowdStrike, a respected cybersecurity firm. That followed a lull in the months after Beijing and Washington reached an accord in 2015 to curtail cyber economic espionage.
The Justice Department has responded with an aggressive series of arrests and indictments.
Federal prosecutors disclosed in October that the FBI had arrested a Chinese intelligence operative in Belgium in a sting operation. Yanjun Xu, a senior officer with the Ministry of State Security, was charged with attempting to commit economic espionage and steal trade secrets from U.S. aerospace companies, including GE Aviation, by paying employees to steal secrets for him.
Yanjun was flown to the U.S. and arraigned in a federal court in Cincinnati, where GE Aviation has spent decades developing jet engines and fan blades. The case marked the first known extradition of a Chinese spy to face U.S. charges. He has pleaded not guilty.
In September, the Justice Department charged a Chicago man with giving Beijing detailed information on engineers and scientists who might make good recruits. In August, a former scientist at GlaxoSmithKline, a pharmaceutical giant, pleaded guilty in Philadelphia to federal charges of stealing data and research on biopharmaceutical products.
The Justice Department also recently charged two Chinese researchers with conspiring to steal rice seeds designed for use in medicine.
Sen. Mark R. Warner (D-Va.), vice chairman of the Senate Committee on Intelligence, applauded the indictment but called for a more comprehensive approach by the Trump administration.
“We have to punch back against China’s malign activities — but we also have to do more than play defense if we’re going to truly check China’s bad behavior,” he said.
Twitter: @DelWilber
More to Read
Get the L.A. Times Politics newsletter
Deeply reported insights into legislation, politics and policy from Sacramento, Washington and beyond. In your inbox twice per week.
You may occasionally receive promotional content from the Los Angeles Times.











