Russian hackers are targeting state and local government networks, U.S. officials say
- Share via
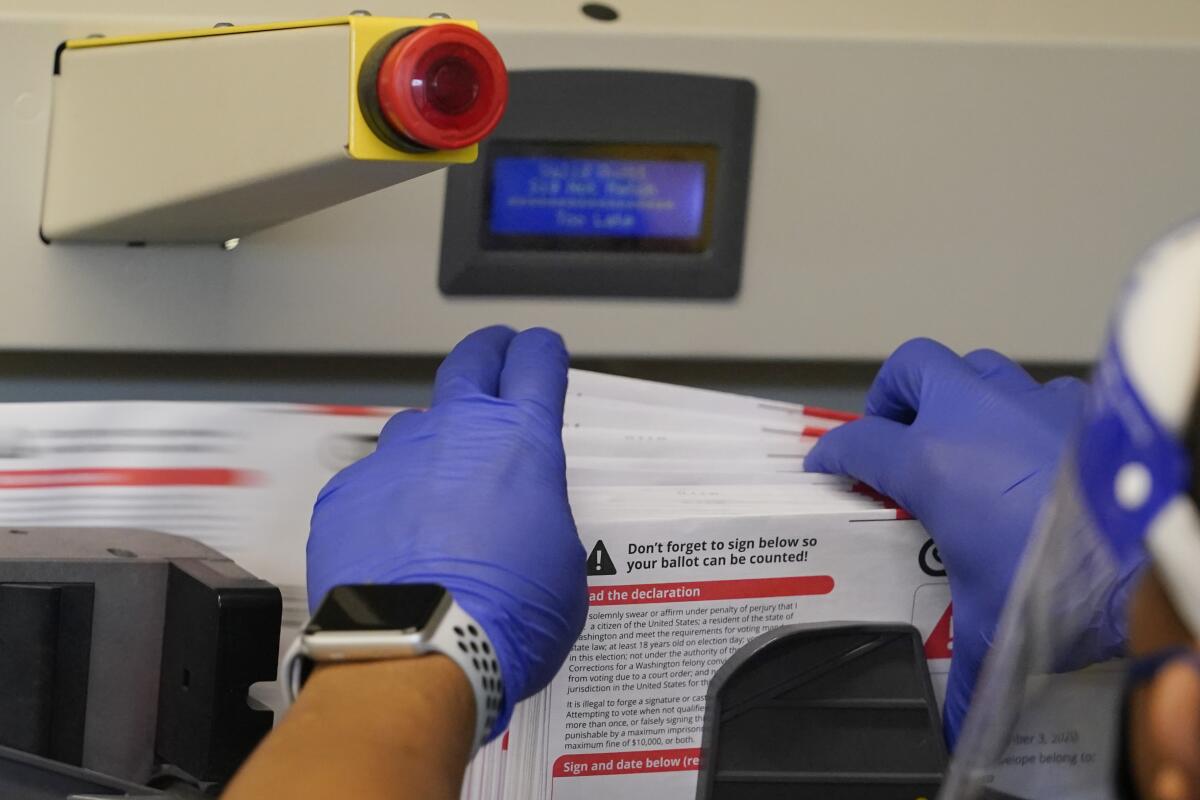
WASHINGTON — U.S. officials said Thursday that Russian hackers have targeted the networks of dozens of state and local governments in the United States in recent days, stealing data from at least two servers. The warning, less than two weeks before the election, amplified fears of the potential for tampering with the vote and undermining confidence in the results.
The alert describes an onslaught of recent activity from Russian state-sponsored hacking groups against state and local networks, some of which were successfully compromised. The advisory from the FBI and the Department of Homeland Security’s cybersecurity agency functions as a reminder of Russia’s potent capabilities and ongoing interference in the election even after U.S. officials publicly called out Iran at a news conference on Wednesday night.
The advisory does not mention any of the specific targets, but officials say they have no information that any election or government operations have been affected or that the integrity of elections data has been compromised.
Iran and Russia have obtained voter registration information and are sending disinformation to Americans ahead of election day, the leaders of U.S. intelligence agencies and the FBI warned.
“However, the actor may be seeking access to obtain future disruption options, to influence U.S. policies and actions, or to delegitimize [state and local] government entities,” the advisory said.
U.S. officials have repeatedly said it would be extremely difficult for hackers to alter vote tallies in a meaningful way, but they have warned about other methods of interference that could include cyberattacks on networks to impede the voting process or the production of spoofed websites or other faked content aimed at causing voters to distrust the results.
A broad concern, particularly at the local government level, has been that hackers could infiltrate a county network and then work their way over to election-related systems unless certain defenses, such as firewalls, are in place. This is especially true for smaller counties that don’t have as much money and IT support as their bigger counterparts to fund security upgrades.
Officials have nonetheless sought to stress the integrity of the vote, with FBI Director Christopher A. Wray saying Wednesday, “You should be confident that your vote counts. Early, unverified claims to the contrary should be viewed with a healthy dose of skepticism.”
U.S. officials warned at a hastily called news conference Wednesday night that Russia and Iran had obtained voting registration information, though such data are sometimes publicly accessible. But most of the focus of that event was on Iran, which officials linked to a series of menacing but fake emails aimed at intimidating voters in multiple battleground states.
Despite that activity, Russia is widely regarded in the cybersecurity community as the bigger threat to the election. The U.S. has said that Russia, which interfered in the 2016 election in part by hacking Democratic email accounts, is interfering again this year partly through a concerted effort to denigrate President Trump’s Democratic opponent, Joe Biden.
U.S. officials attribute the activity to a state-sponsored hacking group variously known in the cybersecurity community as DragonFly and Energetic Bear. The group appears to have been in operation since at least 2011 and is known to have engaged in cyber-espionage on energy companies and power grid operators in the U.S. and Europe, as well as on defense and aviation companies.
Chris Krebs, director of Homeland Security’s Cybersecurity and Infrastructure Security Agency, said Thursday that the alert was issued in regard to scanning of county networks for vulnerabilities, not specifically targeting the election. “There was access in a couple limited cases to an election-related network,” he said.
John Hultquist, the director of threat intelligence at FireEye, said Energetic Bear moved to the top of his worry list when the cybersecurity firm observed it breaking into state and local governments in the U.S. that administer elections, due to it having previously targeted election systems. The Russian hackers have been targeting the industrial control systems of nuclear plants and power grids as well as waterworks and airports in Europe and the United States for years, he said, focused on putting critical infrastructure under threat of disruption.
Hultquist said he does not think Energetic Bear has the ability to directly affect the U.S. vote but fears it could disrupt local and state government networks proximate to the systems that process votes.
“The disruption may have little effect on the outcome. It may be entirely insignificant to the outcome — but it could be perceived as proof that the election outcome is in question,” he said. “Just by getting access to these systems they may be preying on fears of the insecurity of the election.”
More to Read
Sign up for Essential California
The most important California stories and recommendations in your inbox every morning.
You may occasionally receive promotional content from the Los Angeles Times.














