Ransomware attack hits Newhall schools, halting online classes
- Share via
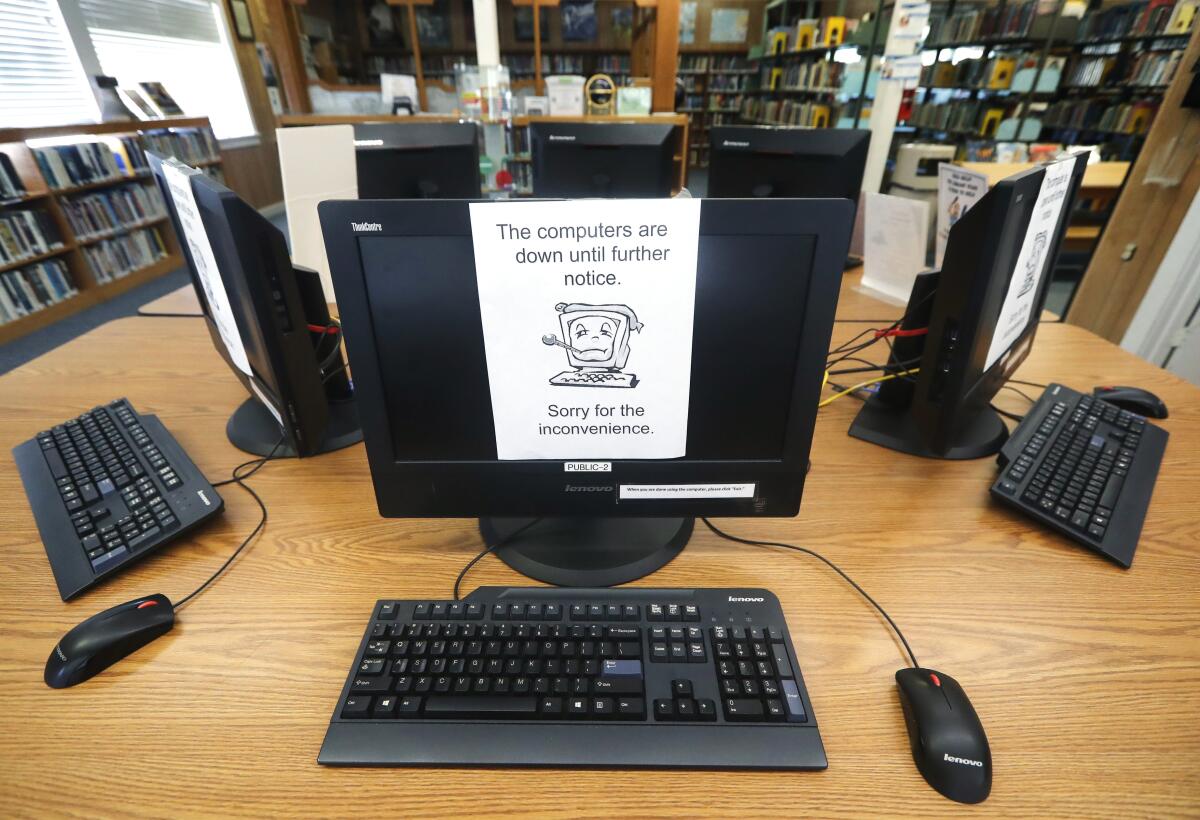
A different sort of virus — ransomware — has taken down the computer system at the Newhall School District, forcing a shutdown of distance learning for some 6,000 elementary school students, officials said.
The weekend attack disabled the district’s server and email, which affected all online learning in the district’s 10 elementary schools.
The Los Angeles County Office of Education defines a ransomware attack “as a form of malware that often targets both human and technical weaknesses by attempting to deny an organization the availability of its most sensitive data and or system.”
“This obviously came at a difficult time for us since we’re 100% digital learning,” Newhall Supt. Jeff Pelzel said Tuesday.
Pelzel believes the attack took place between the late hours of Sunday and early Monday morning.
When Pelzel arrived at the district office Monday morning, he noticed that no emails were being pushed to his smartphone. He then received error messages when he attempted to log into the district’s email server through Outlook and then through a web browser.
According to Pelzel, he consulted the district’s director of IT and the assistant superintendent of business to confirm the attack.
“We noticed there were some error messages on the server and then at the same time we were receiving messages from [schools] saying, ‘hey my screen has this bitlocker,’” said Pelzel, referring to staff members being locked out of their own computers.
At about 7:30 a.m. Monday, the district shut down its servers and sent messages to parents via an emergency notification system and on Instagram that they should avoid the district website, downloads and even emails.
Pelzel informed parents that Monday would be treated as “a non-instructional day for all students” and that the district was working on a resolution.
Later that evening, the district used Instagram to announce a return to pencil, paper and textbook learning that included 180 minutes of activities for preschoolers and kindergartners, 230 minutes for first- through third-graders and 240 minutes for fourth- through sixth-graders.
The youngest students were asked to spend 30 minutes reading with their family as one exercise, for instance, while first- through third-graders were slated to spend 30 minutes handwriting a letter to a friend and fourth- through sixth-graders were to participate in 30 minutes of step-counting, marching in place or dancing.
Pelzel said similar instruction was being developed between the administration and teachers union for Wednesday, but he was uncertain how long the independent learning would continue.
The district has hired an outside forensics team to investigate the cause of the attack, survey the damage and offer an estimate of when normal online learning could resume. Pelzel said he hoped to have more information by Wednesday evening.
Greg Lindner, the county Office of Education’s chief technology officer, believes this is the first such ransomware attack of a county school district this year, although that’s with a disclaimer.
“County districts are not obligated to tell us,” Lindner said of cyberattacks. “If they need help, they’ll ask us or, in this case, if we hear about something, we’ll contact them.”
Last month, the Rialto Unified School District in San Bernardino County, suffered a malware attack.
Lindner said four Los Angeles County districts reported attacks to the Office of Education last school year, which pushed the governing body to create a county cybersecurity committee in March. The group’s goal is to provide training in cyberattack prevention.
“We have to be prepared because these attackers want money,” Lindner said. “It’s big business.”
Lindner said about two-thirds of attacks take place through email and phishing scams, while downloads and hacking are also involved.
As of Tuesday, Pelzel said there has not been any monetary demands.
While the district backed up its server, Pelzel said it’s uncertain if it, too, was compromised.
“There’s a lot more information we need to find out before we can move forward,” he said.
More to Read
Sign up for Essential California
The most important California stories and recommendations in your inbox every morning.
You may occasionally receive promotional content from the Los Angeles Times.














